Cybercriminals are constantly finding new ways to steal your data. As people become more aware of common threats like phishing links, fake websites, fraudulent emails and impersonation scams, attackers are becoming more creative in their approach.
One of the newer methods they are using involves targeting USB flash drives. It may seem surprising that they would focus on something as simple as a flash drive, but the data it holds can be valuable.
Plus, flash drives can be used to spread malware to other devices.

A person plugging in a USB flash drive to a laptop (Kurt “CyberGuy” Knutsson)
Why target USB flash drives?
USB drives are ubiquitous in workplaces, especially in environments with air-gapped systems or restricted internet access, such as those in government and energy sectors. This makes them an easy target for data theft and malware propagation. Often, these drives store sensitive files that are not available on networked systems.
WHAT IS ARTIFICIAL INTELLIGENCE (AI)?
When infected, USB drives can spread malware not just within a single organization but also across multiple entities if shared. These attacks don’t rely on network vulnerabilities, allowing them to bypass traditional security tools.

USB Flash drive plugged into a laptop (Kurt “CyberGuy” Knutsson)
200 MILLION SOCIAL MEDIA RECORDS LEAKED IN MAJOR X DATA BREACH
How hackers are targeting your USB drives
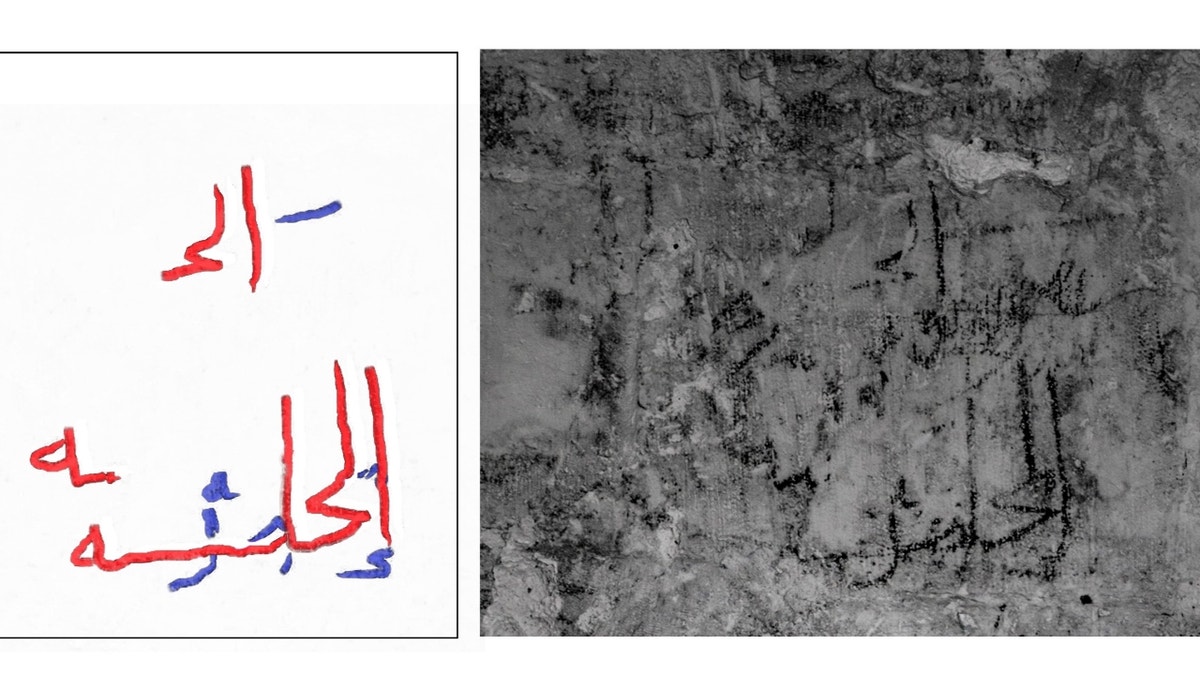
As reported by Kaspersky’s Securelist, a cybersecurity research platform, hackers are using USB drives to spread malware in ways that can easily bypass traditional security systems. One group, known as GOFFEE, kicks off its attacks with targeted phishing emails. These emails often carry infected RAR files or Office documents with harmful macros. Once opened, they install sneaky programs like PowerModul and PowerTaskel on the victim’s system.
These tools don’t just sit around. They lay the groundwork for more attacks. PowerModul, in particular, plays a big role. It’s a PowerShell script introduced in 2024 that talks to a command-and-control (C2) server. From there, it can download and run other tools, including two especially dangerous ones, FlashFileGrabber and USB Worm.
FlashFileGrabber is made to steal data from USB drives. It can either save stolen files locally or send them back to the hacker’s server. Then there’s USB Worm, which infects any USB drive it finds with PowerModul, turning that drive into a tool for spreading malware to other systems.
What makes this method effective is that USB drives are often shared between people and offices. That physical movement allows the malware to spread even without an internet connection. The malware hides original files on the USB and replaces them with malicious scripts disguised as normal-looking shortcuts. When someone clicks one of these, they unknowingly trigger the infection.
GET FOX BUSINESS ON THE GO BY CLICKING HERE
Illustration of a hacker at work (Kurt “CyberGuy” Knutsson)
MALWARE EXPOSES 3.9 BILLION PASSWORDS IN HUGE CYBERSECURITY THREAT
4 practical ways to stay safe from USB-targeted attacks
1. Don’t plug in unknown USB drives: It might sound obvious, but this is one of the most common ways malware spreads. If you find a USB drive lying around or someone gives you one you weren’t expecting, avoid plugging it into your system. Attackers often rely on human curiosity to get the malware onto your machine.
2. Be extra cautious with email attachments: GOFFEE’s campaigns often begin with phishing emails carrying malicious RAR files or Office documents with macros. Always double-check the sender’s address and never open unexpected attachments, especially if they ask you to “enable macros” or come from unknown contacts. When in doubt, confirm through a different channel.
3. Avoid clicking on suspicious links and use strong antivirus software: Many attacks like GOFFEE’s start with emails that look legitimate but contain malicious links. These links might lead you to fake login pages or silently download malware that sets the stage for USB-targeting tools like PowerModul.
The best way to safeguard yourself from malicious links that install malware, potentially accessing your private information, is to have strong antivirus software installed on all your devices. This protection can also alert you to phishing emails and ransomware scams, keeping your personal information and digital assets safe. Get my picks for the best 2025 antivirus protection winners for your Windows, Mac, Android and iOS devices.
4. Scan USB drives before use: The USB Worm infects USB drives by hiding original files and planting malicious scripts disguised as shortcuts, which trigger PowerModul when clicked. FlashFileGrabber also steals files silently from USBs, often going unnoticed. Always scan USB drives with updated antivirus software before opening any files. Use a reputable security tool to check for hidden scripts, unusual shortcuts or unexpected executables. If files appear renamed or hidden, don’t click them until verified safe.
DATA REMOVAL DOES WHAT VPNS DON’T: HERE’S WHY YOU NEED BOTH
Kurt’s key takeaway
Cybercriminals thrive where convenience meets oversight. However, it’s worth considering why USBs remain such a soft target. They’re not just storage but a cultural artifact of workplaces, especially in high-stakes sectors like energy or government, where offline data transfer feels safer than the cloud. But that trust is a blind spot. Attackers like GOFFEE don’t need zero days because they can exploit human habits such as sharing drives, skipping scans and clicking without thinking.
How often do you plug in a USB drive without scanning it first? Let us know by writing us at Cyberguy.com/Contact
CLICK HERE TO GET THE FOX NEWS APP
For more of my tech tips and security alerts, subscribe to my free CyberGuy Report Newsletter by heading to Cyberguy.com/Newsletter
Ask Kurt a question or let us know what stories you’d like us to cover
Follow Kurt on his social channels
Answers to the most asked CyberGuy questions:
New from Kurt:
Copyright 2025 CyberGuy.com. All rights reserved.