Remember those ancient clay structures from history class? Well, clay is making a grand re-entrance into the world of construction, and it’s undergone a high-tech makeover. Thanks to a cutting-edge process called impact printing, clay might just be the building material of the future.
GET SECURITY ALERTS, EXPERT TIPS – SIGN UP FOR KURT’S NEWSLETTER – THE CYBERGUY REPORT HERE

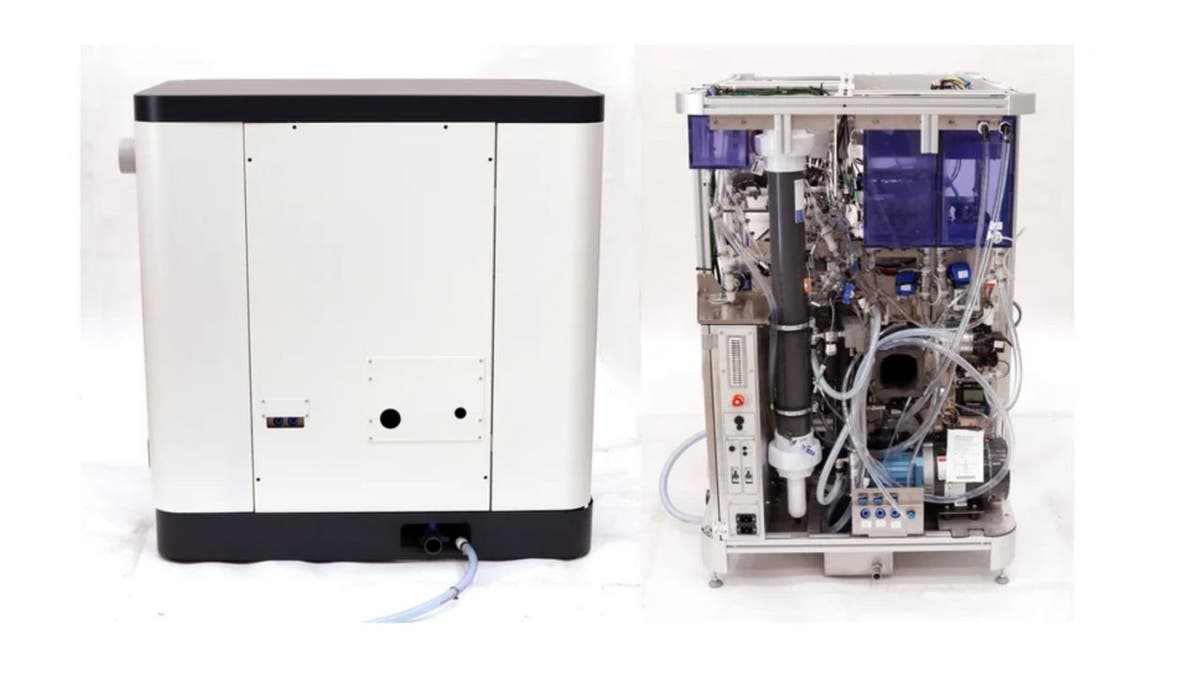
Impact printing with clay (ETH Zurich) (Kurt “CyberGuy” Knutsson)
Move over, concrete: There’s a new building material in town
By now, you’ve probably heard about 3D-printed concrete houses. They’re quick, cheap and produce less waste than traditional building methods. But let’s face it, concrete has its downsides. It needs time to harden, and the cement industry is a major contributor to greenhouse gas emissions. Enter clay, stage left.

Impact printing with clay (ETH Zurich) (Kurt “CyberGuy” Knutsson)
LEGO-LIKE CONSTRUCTION BLOCKS MADE FROM PLASTIC WASTE CAN STAND UP TO NATURE’S FURY
Introducing impact printing with clay
A team of clever scientists at ETH Zurich, led by Dr. Lauren Vasey, has developed a new way to build with clay. They’ve created a special mix of clay, silt and a secret ingredient (a “common waste product” from their industry partner). But here’s where it gets exciting: instead of slowly extruding the material, they shoot it at high speeds using a machine that could one day be brought right to the construction site.
HOW TO REMOVE YOUR PRIVATE DATA FROM THE INTERNET

Impact printing with clay (ETH Zurich) (Kurt “CyberGuy” Knutsson)
CONSTRUCTION WORKERS BEING REPLACED BY AI ROBOT BRICKLAYERS
The art of blob building
Picture this: Blobs of clay mixture flying through the air at speeds up to 32.8 feet per second. When these blobs hit their target, they stick together, gradually forming walls, columns or whatever structure you fancy. It’s like watching a high-speed game of clay Tetris.

Impact printing with clay (ETH Zurich) (Kurt “CyberGuy” Knutsson)
3D PRINTER CONSTRUCTS STUNNING DATA CENTER HANDS-FREE IN 140 HOURS
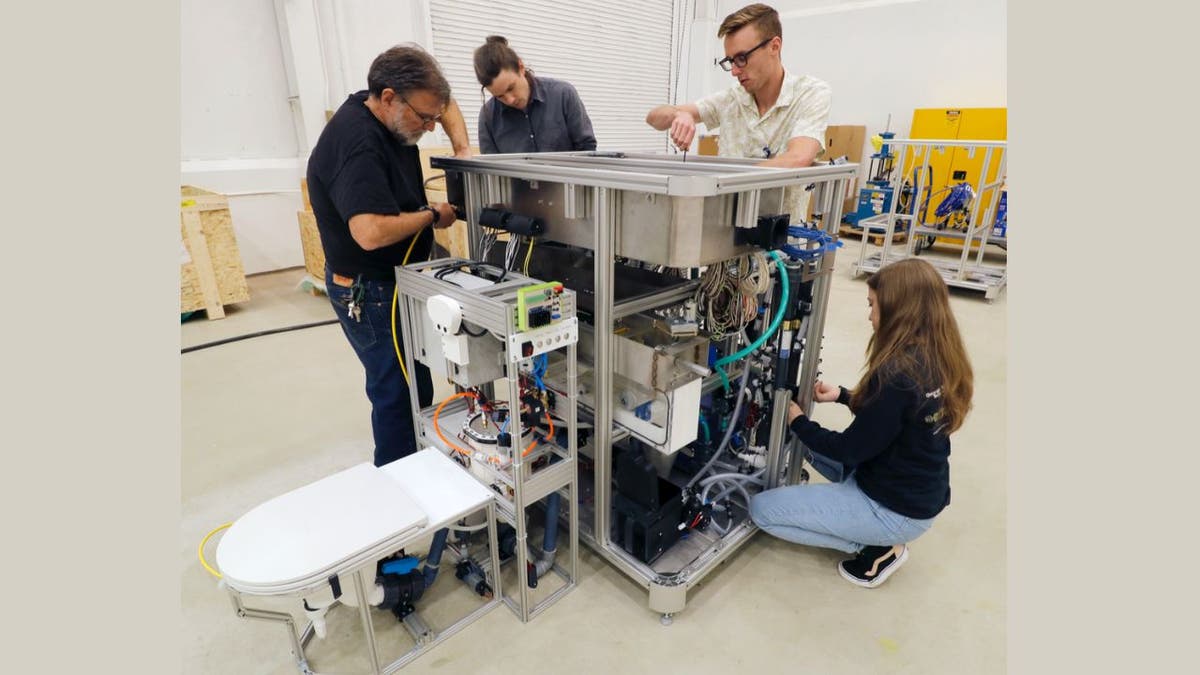
A robotic arm provides the finishing touches
If you’re not into the “bunch-of-blobs” aesthetic (though it could be the next big thing in interior design), don’t worry. The researchers have thought of that, too. A robotic arm with a rotary tool can smooth out the surfaces, giving you that sleek, modern look.

Impact printing with clay (ETH Zurich) (Kurt “CyberGuy” Knutsson)
What’s next for impact printing?
The team at ETH Zurich isn’t stopping at simple structures. They’re working on ways to integrate supportive elements into the clay as it’s being deposited and developing fancy software to guide the construction of more complex buildings. They’re even thinking about mounting the printing rig on an autonomous excavator. Imagine a robot building your house while you sip lemonade and watch.
SUBSCRIBE TO KURT’S YOUTUBE CHANNEL FOR QUICK VIDEO TIPS ON HOW TO WORK ALL OF YOUR TECH DEVICES

Impact printing with clay (ETH Zurich) (Kurt “CyberGuy” Knutsson)
Kurt’s key takeaways
Impact printing with clay is still in its early stages, but it’s showing incredible promise. It’s fast, doesn’t require cement and uses readily available materials. Plus, it’s a sustainable alternative to concrete construction. As we face increasing pressure to reduce our carbon footprint, technologies like this could play a crucial role in the future of construction. Who knows? In a few years, you might be telling your real estate agent, “I’m looking for a nice three-bedroom, two-bath impact-printed clay home.”
After reading about impact printing technology, would you feel comfortable living in a clay house? Let us know by writing us at Cyberguy.com/Contact.
For more of my tech tips and security alerts, subscribe to my free CyberGuy Report Newsletter by heading to Cyberguy.com/Newsletter.
Ask Kurt a question or let us know what stories you’d like us to cover.
Follow Kurt on his social channels:
Answers to the most asked CyberGuy questions:
New from Kurt:
Copyright 2024 CyberGuy.com. All rights reserved.