NEWYou can now listen to Fox News articles!
Attorney Matt Murphy is sharing insight into what the road ahead looks like for Nick Reiner after he was taken into custody for allegedly murdering his parents, beloved Hollywood actor and director, Rob Reiner, and his wife, Michele Reiner.
When speaking with Fox News Digital, Murphy explained that discovery is still ongoing in this case, saying Nick’s lawyer, Alan Jackson, “needs to carefully review as much discoveries as he can get,” so that he can “confidently decide” if his client should “just plead not guilty” or to submit a “guilty by reason of insanity plea.”
“So continuing an arraignment, there’s nothing unusual about that. And it’s also important to remember that Nick Reiner not being transported – there’s no verdict on that. There’s no mental health professional that is making that call. The defense has the unilateral ability to, like I said, declare a doubt. And they can say, ‘My client isn’t ready to do this yet,’ and at this stage, the court basically has to take them at their word.”
Murphy says Jackson now has to “get his clients stabilized [and] communicative,” adding that the next step in the process is to “hurry up and wait.” He added that he “wouldn’t be surprised to see this arraignment continued” a few times, until Jackson “decides whether or not he’s going to enter a plea.”
Murphy says the case is still in the discovery phase. (Laura Cavanaugh/FilmMagic)
ROB REINER AND WIFE MURDERED: TIMELINE SHOWS ARGUMENT WITH SON NIGHT BEFORE DEATHS
He explained that the defense will likely ask the court for time to evaluate everything, and knowing that this case has the potential for the death penalty, Murphy emphasized that he wouldn’t “want the public’s desire for an outcome ever to influence the constitutional rights of a criminal defendant” and therefore would support that.
“The defense will then prepare what’s known as a live-z packet, or in Los Angeles County, they call it a live z hearing. He’s gonna accumulate as much information as he can regarding factors in mitigation,” he explained. “In the death penalty analysis, it’s about factors in aggravation versus factors in mitigation. And some big factors in mitigation Alan Jackson’s gonna argue are, the history of substance abuse, the family dynamics, the fact that these weren’t strangers, these were his parents that knew him, et cetera, et cetera et cetera.”
WATCH: ATTORNEY MATT MURPHY SHARES WHAT THE NEXT STEPS ARE IN NICK REINER’S CASE
Jackson will then present the packet to Los Angeles County District Attorney, Nathan Hochman, and his staff.
LEGENDARY DELI MADE FAMOUS BY ROB REINER’S MOST ICONIC MOVIE SCENE
“Nathan Hockman will then make a decision regarding whether they’re gonna seek the death penalty or whether they are simply gonna seek life without possibility of parole,” Murphy said. “And again, my prediction is they’re going to seek LWOP. They’re gonna to seek life without possibility parole. But I could be surprised. I’ve been wrong before.”
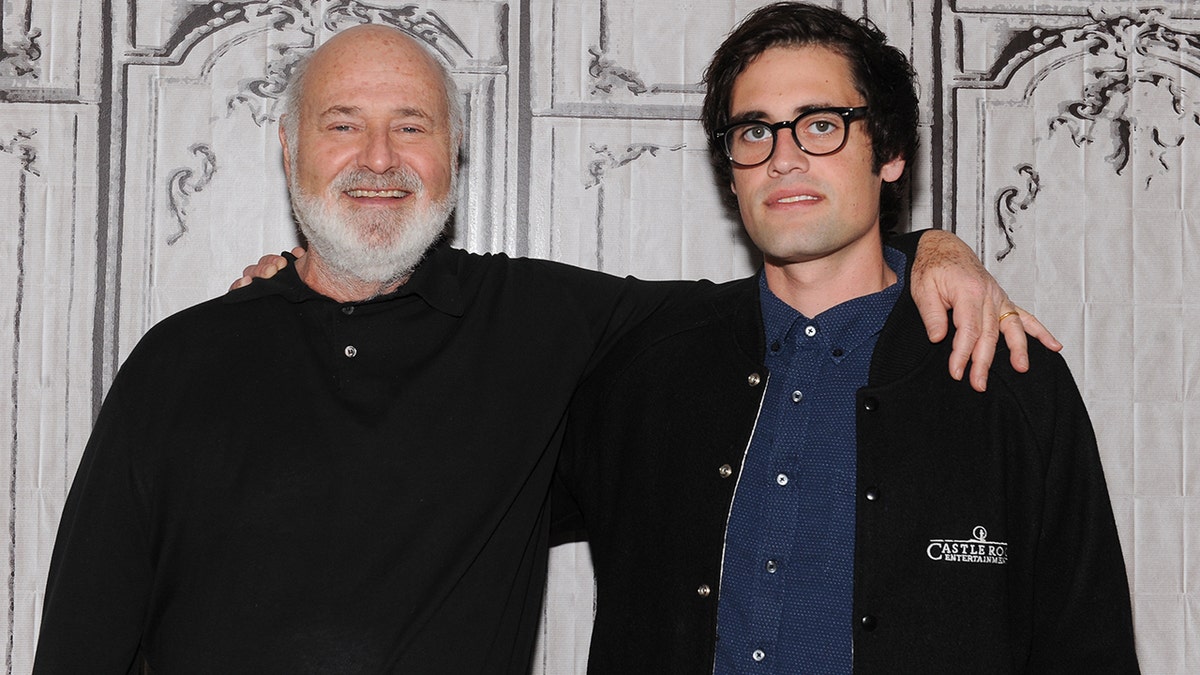
Murphy predicts Nick will receive a sentence of life in prison without the possibility of parole. ( Rommel Demano/Getty Images)
After Nick was detained under suspicion of murdering his parents, his history with addiction and mental health struggles have resurfaced.
Murphy predicts Jackson will come in with “some sort of mental health defense based on the addiction,” and his struggles with mental health issues, but said there is a difference as far as “organic mental illness” goes. Organic mental illness encompasses illnesses such as “schizophrenia that develops, that is no fault of the defendant.”
NICK REINER WILL BE CHARGED IN ROB REINER, MICHELE REINER’S DEATHS
“In other words, they get sick, they get mentally ill, and then they try to self-medicate, or they get into drugs as a result of that,” Murphy said. “I haven’t heard any of that yet on Nick Reiner.”
He went on to compare Nick’s case to another he worked in Orange County, California, which involved a young man with documented organic mental illness, who murdered his parents and was deemed legally sane and found guilty.
Murphy compared Nick’s case to a similar case he worked in Orange County. (Mona Edwards)
“California uses what’s known as The McNaughton Rule,” Murphy said. “The McNaughton Rule is about 150 years old, and it basically stands for the proposition that if the criminal defendant understands the nature and quality of their acts, the nature and the quality of the acts at the time they commit the murder, then they are legally responsible even if they’re high, even if their drunk, even they’re suffering from mental illness.”
WATCH: ATTORNEY MATT MURPHY SAYS ALAN JACKSON IS ‘UP AGAINST A TOUGH ONE’ DEFENDING NICK REINER
ROB REINER AND WIFE MICHELE WERE FOUND DEAD IN THEIR BEDROOM: LAPD
“So the way we would explain it to our juries is if the devil pops up on the guy’s shoulder and says ‘hey go over there and stab that banana,’ the person does not understand that they’re killing a human being,” he continued. “In other words, they don’t understand the nature and quality of their acts. However, if it’s the devil pops up on your shoulder and says, go kill those people or I’m going to turn you into a frog, you still under the law have a moral and legal responsibility to tell the devil no.”
WATCH: ATTORNEY MATT MURPHY SAYS IT WOULDN’T SHOCK HIM TO SEE ‘A BATTLE OF THE EXPERTS’ DURING THE NICK REINER TRIAL
Due to these factors, Murphy said that “as good as Alan Jackson is, he’s up against a tough one,” adding that being intoxicated is not a “true defense to murder,” because if it was, “nobody would ever be held accountable for murder.”
In terms of the actual trial, Murphy says that it’s possible that the defense will “declare a doubt regarding the mental competency” of their client, after which “the court will appoint two experts to do an evaluation,” and then “you wind up with this very long procedural process.”
CLICK HERE TO SIGN UP FOR THE ENTERTAINMENT NEWSLETTER
Murphy predicts the defense will “declare a doubt” about Nick’s mental competency. (Michael Buckner/Getty Images for Teen Vogue)
“Doctors will evaluate Nick Reiner and render their opinions,” he said. “And then if he’s found to be incompetent, then he goes to a mental health facility. It’s locked down for treatment and medication so that he will come back. And sometimes you see, it’s almost like a game, a ping pong, where the mental health professionals will certify somebody for competency, send them back to court, and then the defense lawyer will declare a doubt again.”
Murphy made it clear that the investigation doesn’t stop when charges are filed and that both the defense and the prosecution will conduct “a very dedicated [and a] very professional investigation.”
WATCH: ATTORNEY MATT MURPHY PREDICTS NICK REINER’S TRIAL ‘IS GOING TO BE A VERY LONG PROCESS’
A video of Nick walking into a gas station and buying a drink following the murder has since surfaced online, and he allegedly was “acting bizarrely” prior to the murders while at Conan O’Brien’s holiday party, two things Murphy says “can cut both ways.”
“With a very skilled trial lawyer like Alan Jackson, he’s going to argue, ‘Look, that means he doesn’t know that he did anything wrong,'” Murphy explained. “And what the prosecution is going to say is. ‘Look, that guy, clearly, he’s not howling at the moon. He knows how to use a credit card. He knows that he’s dealing with a person behind the register.’ And truly, under the law, it’s a very, very strict standard under the McNaughton rule.”
LIKE WHAT YOU’RE READING? CLICK HERE FOR MORE ENTERTAINMENT NEWS
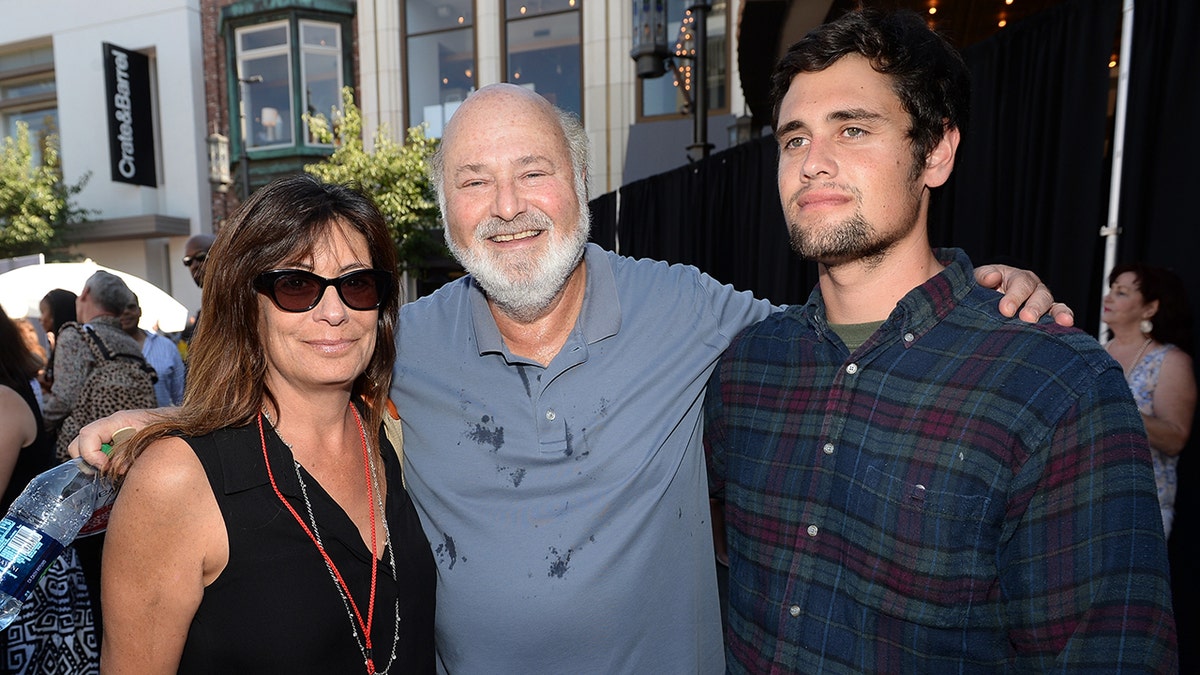
Murphy said it is clear Rob and Michele Reiner loved their son. (Stefanie Keenan)
Murphy ended by acknowledging that “addiction hits almost every family in America,” and that so many people know someone like Nick, adding about Nick that “I think it’s very clear that he was loved by his parents.”
“The number we keep seeing is 17 stints in rehab. I mean, that’s two parents that really love their son,” Murphy said. “Even to the point that he’s 32 years old and they’re bringing him to Conan O’Brien’s party. So he had a lot of advantages in life, and he’s previously described himself as being a spoiled rich kid. So we’ll see where this goes. This is gonna be a very, very interesting case to watch.”
CLICK HERE TO DOWNLOAD THE FOX NEWS APP
Lori Bashian is an entertainment writer for Fox News Digital.