With vacation planning, most people fall into two camps: those who love planning and those who hate it.
Artificial intelligence tools like GuideGeek, developed by Matador Network and accessible via Meta’s Messenger app, offer a glimpse into a future where vacation planning is as simple as sending a text.
Yet, as we lean into this new era, it’s clear that these amazingly powerful tools come with their own set of quirks.

Man walking through airport with passport in his hand (Kurt “CyberGuy” Knutsson)
AI travel ‘hallucinations’ can derail a trip
Take, for instance, the phenomenon known as “AI hallucinations.” These occur when the AI, attempting to fill gaps in its knowledge, invents answers. A classic example unfolded when an AI-powered assistant was asked about travel details for “Crete Freeze” instead of “Crete, Greece”. Instead of clarifying the query, the AI crafted a detailed story about a non-existent ice cream parlor in Pittsburgh. While creative, such responses aren’t particularly useful when you’re trying to plan an actual trip.

A couple on vacation (Kurt “CyberGuy” Knutsson)
MORE: 5 GREAT TIPS FOR PLANNING YOUR NEXT TRAVEL GETAWAY
When tiny missed details turn into big trouble
This isn’t an isolated incident. Across the travel industry, AI tools have mistakenly concocted false job histories and even non-existent travel destinations. This tendency can lead to significant travel planning errors, such as suggesting routes that don’t exist or accommodations that are the stuff of fiction.
Why does this happen? AI systems, particularly those based on generative models, strive to provide answers for every query. In doing so, they sometimes create plausible but incorrect information. While these errors are often corrected quickly, they highlight an important aspect of using AI in travel planning: verification is key.

Family at the beach (Kurt “CyberGuy” Knutsson)
MORE: TRAVELING? BRING THIS TRIPLE PROTECTION FOR SAFER ONLINE BANKING
Embracing the new AI travel planning experiment
Matador Network has taken steps to mitigate these errors by introducing stringent checks and balances for GuideGeek. They’ve reduced the occurrence of hallucinations significantly, from a startling 14% down to a more manageable 2%. They achieved this by enhancing the AI’s training and integrating real-time data from reliable sources like Skyscanner and Expedia.
Despite these improvements, the responsibility ultimately falls on the travel planner to double-check all AI-generated plans. When using AI tools like GuideGeek, it’s prudent to verify the details of your itinerary as you would with a travel agent. Check flight schedules, hotel bookings and travel routes against trusted sources.

A family at the beach (Kurt “CyberGuy” Knutsson)
Verify any travel plans, whether from AI or a human expert
Incorporating AI into travel planning requires a balanced approach. While these tools can efficiently handle vast amounts of data and provide quick responses, their current propensity for errors cannot be overlooked. People should approach AI-generated travel plans with a healthy dose of both excitement and skepticism, reviewing and confirming details to avoid potential pitfalls.
WHAT IS ARTIFICIAL INTELLIGENCE (AI)?

Dad and daughter at the beach (Kurt “CyberGuy” Knutsson)
AI trip planning can open doors you never knew to knock on
The process of integrating AI into travel planning is undoubtedly exciting, and it promises a more streamlined and accessible future for travelers.
Matador Network CEO Ross Borden points to the benefits of AI travel planning, saying, “We all know that typical experience of booking travel online – you’ve got 30 browser tabs open and a headache. GuideGeek is a travel genius that makes creating detailed travel plans much faster and more personalized. As the AI learns about you, the recommendations get more tailored to your interests and how you travel.”
GET FOX BUSINESS ON THE GO BY CLICKING HERE
I checked AI on one of my favorite Hawaiian destinations for trip-planning ideas known mostly by the locals and deeply entrenched experts. AI was able to identify a really fun area to hike in Kaua’i, along with the little-known secret of how to find parking nearby. I seldom see tourists there, and AI is about to change that. What it didn’t know to tell me is what happens if a common rain shower interrupts the hike, turning the elevated trail into a treacherous trench of mud – something a local or expert may have warned you about.

GuideGeek website (GuideGeek)
MORE: THE BEST TRAVEL GEAR FOR 2024
How to plan travel with AI using GuideGeek
Unlike other travel guides, if you have Instagram, Facebook Messenger or WhatsApp, you do not need to download a separate app to use GuideGeek. All you need to do is go to the main GuideGeek website. In the app you likely have already downloaded, you can either click the link or scan the QR code, which will launch GuideGeek on your designated app.
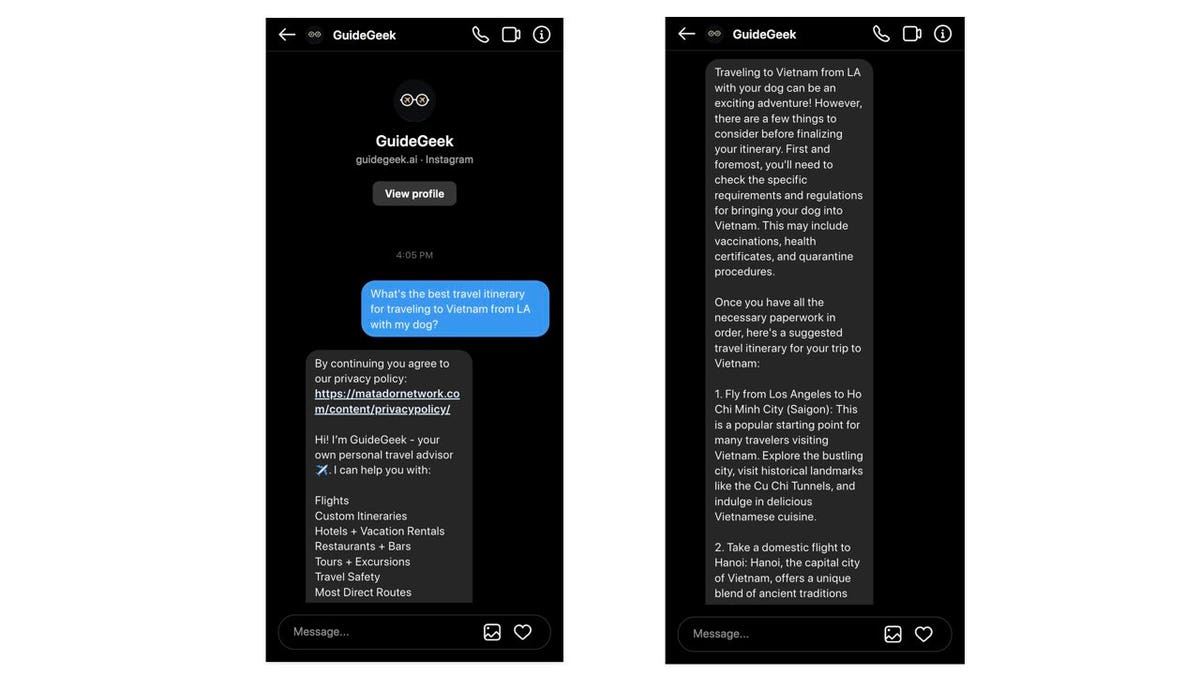
GuideGeek screens on Instagram (GuideGeek)
MORE: 5 GREAT TIPS FOR PLANNING YOUR NEXT TRAVEL GETAWAY
Chat with GuideGeek: Your personal, nonhuman AI travel assistant on Instagram
For instance, if you click “Open on Instagram,” GuideGeek will begin a direct message on the Instagram account you have on your device. You can ask any sort of travel question, and it’ll respond with an answer as a message.
The best part is that once you have opened it, you can continue to dialogue with GuideGeek for other areas of your travel needs – just don’t delete the chat window with GuideGeek. Of course, if you do, it is just as easy to restart another message with GuideGeek.
GuideGeek AI on Facebook (GuideGeek)
MORE: BEST TRAVEL ADAPTERS OF 2024
Planning travel with GuideGeek vs Google
What’s the difference between using GuideGeek instead of googling your questions? Targeted answers, so you’re not digging around many websites for that one piece of travel information you’re looking for. Additionally, the use of the Matador Network is hooking you up with an established online travel publication located in San Francisco with more than 80 million monthly visitors and 16 million social media followers.
Kurt’s key takeaways
With so much travel information online, it can be difficult to parse through all the data. And sometimes, too much information can actually create decision fatigue. Instead of trying to cobble together an itinerary from your neighbors, family, friends and the internet, you can use AI to pull together an exciting trip – just be sure to check each little detail for accuracy before packing your bags.
CLICK HERE TO GET THE FOX NEWS APP
Have you utilized AI to help start or finish travel planning? If you could have a travel agent available on demand, would you use it? Let us know by writing us at Cyberguy.com/Contact.
For more of my tech tips and security alerts, subscribe to my free CyberGuy Report Newsletter by heading to Cyberguy.com/Newsletter.
Ask Kurt a question or let us know what stories you’d like us to cover.
Answers to the most asked CyberGuy questions:
Copyright 2024 CyberGuy.com. All rights reserved.