A new hacking threat is targeting crypto users via Calendly, a popular meeting-scheduling app. This is a serious issue that could compromise your security and privacy, so you need to be aware of how it works and how to protect yourself.
Calendly app (Calendly) (Kurt “CyberGuy” Knutsson)
Hackers are posing as crypto investors via Calendly
The way this particular threat works is rather straightforward, yet sneaky. To start, many people in the crypto world are seeking investments to support their crypto start-up ideas or something related.
People like this need to be active in crypto communities and investment spaces to connect with the right people to support them. It’s not uncommon for these people to have a link to schedule a meeting with them on their profile, via Calendly, a popular scheduling app not just for people in cryptocurrency but for anyone.
Calendly app (Calendly) (Kurt “CyberGuy” Knutsson)
How the hacker infiltrates the target’s device
Unbeknownst to the soon-to-be victim, these hackers are taking advantage of these individuals by posing as crypto investors, the exact kind of people these folks want to get in touch with. When they book a meeting on this person’s calendar, they add a meeting link that runs a script that installs malware on macOS systems.
A real-life example of how crypto impersonators lure victims
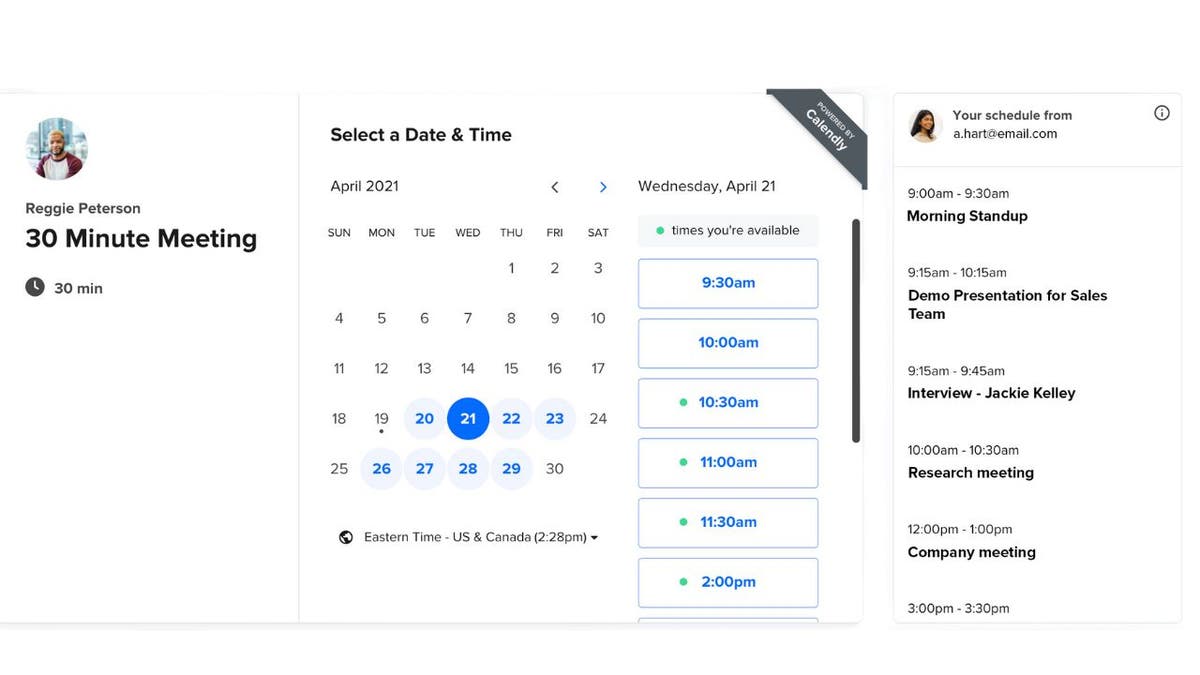
This happened to one unlucky person in this situation. The hacker reached out via Telegram – an encrypted messaging app – and asked about booking a meeting. The person sent the “investor” their Calendly link, and on the day of the meeting, went to the meeting link that the “investor” had added. In most cases, this is normal – a link to a Zoom or Google Meet is not unusual. And because the user had already spoken to the person via Telegram and seemed legitimate, there was no reason to think twice about this.
The sinister scheme was revealed when links failed
Only when the person went to click the link and when the “investor” didn’t show up, did he contact him on the same Telegram thread. The “investor” apologized for the inconvenience and sent a new link, explaining there was an issue with IT.
However, the link still did not work, and the meeting never happened, with the “investor” asking to reschedule. It dawned on the person a little afterward that this may have been a hack attack, via an Apple Script (file extension “.scpt”) that downloads and executes a malicious Trojan made to run on macOS systems.
Hacker Google Meet request (SlowMist) (Kurt “CyberGuy” Knutsson)
MORE: STEALTHY BACKDOOR MAC MALWARE THAT CAN WIPE OUT YOUR FILES
How quick action foiled a Mac malware attack
Because the person who was the target of this attack promptly backed up their data upon realizing the attack, it prevented the loss of evidence regarding the actual malware downloaded onto their macOS. Cybersecurity firms were able to analyze the script information, which led them to identify similarities with previous attacks carried out by the same group and warn the public.
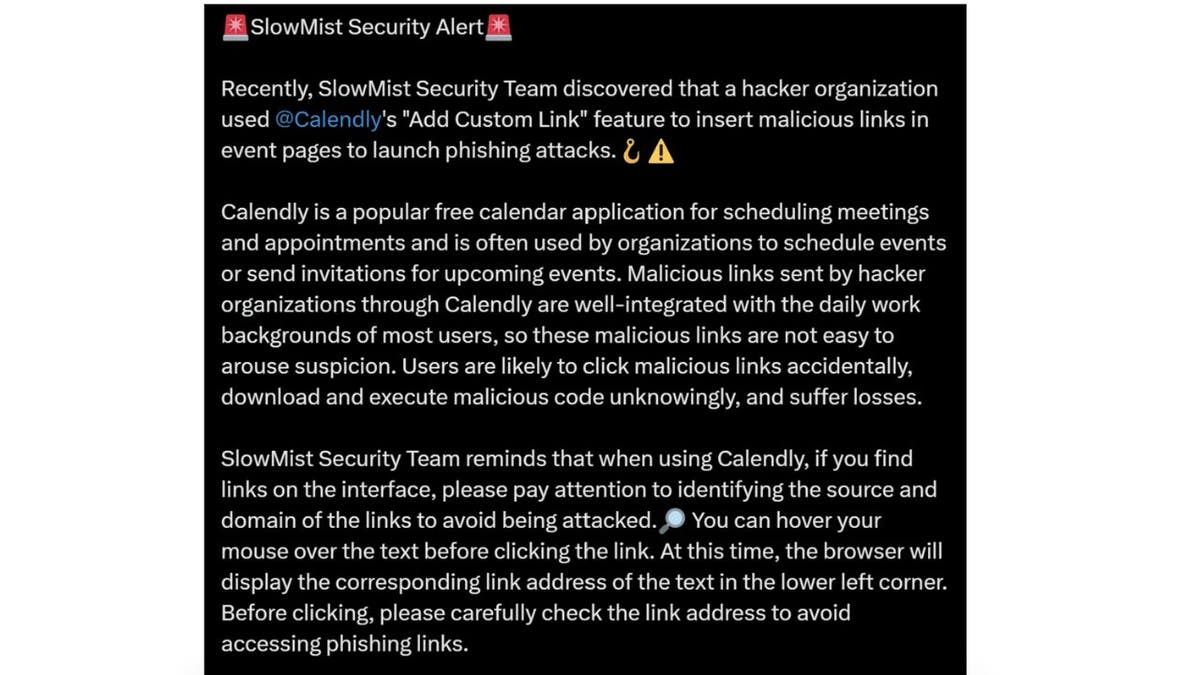
Security alert (SlowMist) (Kurt “CyberGuy” Knutsson)
MORE: HOW TO PROTECT YOUR MAC FROM THE NEW METASTEALER MALWARE
The perpetrators are a hacker group from North Korea
A cybersecurity firm discovered a phishing attack in 2023 that was carried out by state-sponsored hackers from North Korea, specifically a subgroup of the notorious Lazarus group. This group typically targets financial gains, aiming to steal money or cryptocurrency to fund the North Korean military regime.
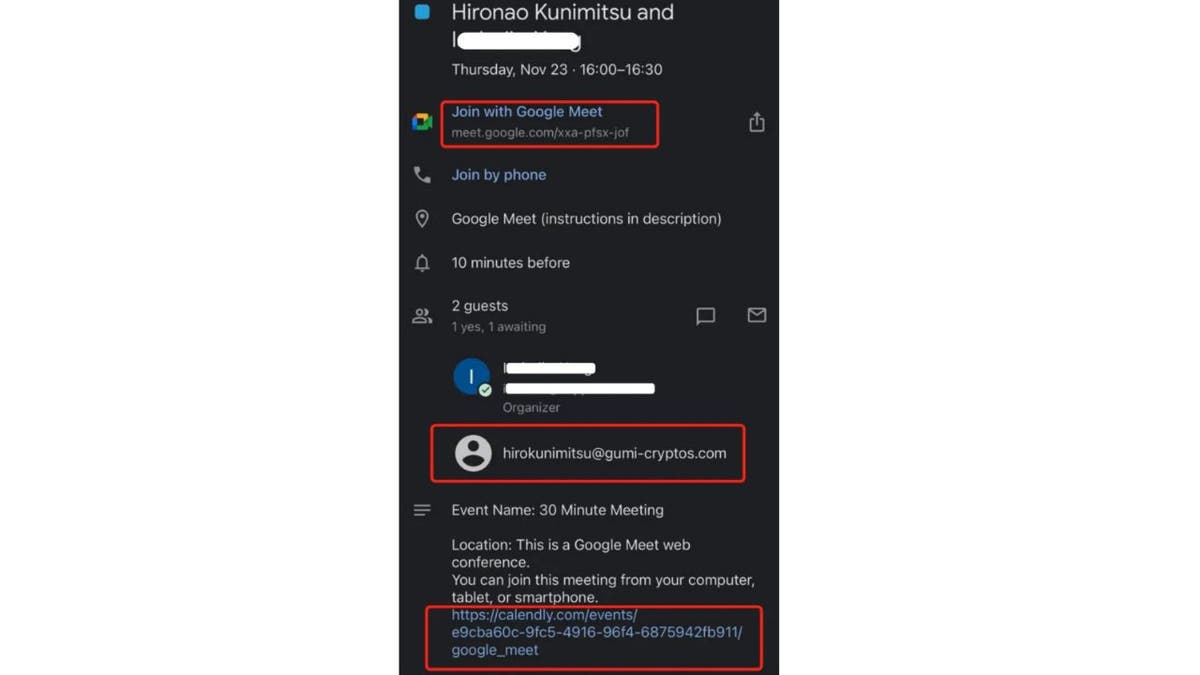
In this particular attack, the North Korean hackers exploited the “Add Custom Link” feature within the Calendly meeting scheduling system on event pages to insert malicious links and initiate phishing attacks. They also employ similar tactics on Telegram.
This incident underscores the importance of vigilance and robust security measures to safeguard against cyberthreats, especially those originating from state-sponsored actors.
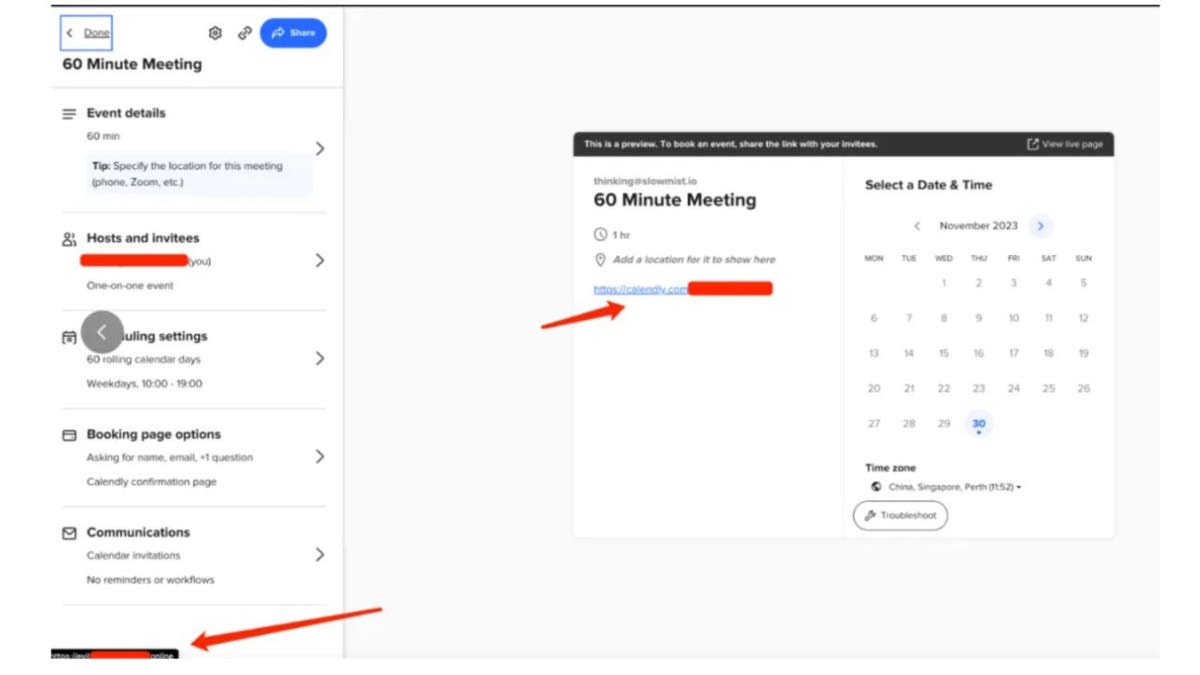
Add Custom Link feature (SlowMist) (Kurt “CyberGuy” Knutsson)
Calendly’s response to malware attacks
We reached out to Calendly, and their CISO (chief information security officer), Frank Russo, provided us with this statement.
“We’re aware of these types of social engineering attacks by cryptocurrency hackers. This attack violates our Terms of Use, and accounts are immediately terminated when discovered or reported. To help prevent these kinds of attacks, our security team and partners have implemented a service to automatically detect fraud and impersonations that could lead to social engineering. We are also actively scanning content for all our customers to catch these types of malicious links and to prevent hackers earlier on. Additionally, we intend to add an interstitial page warning users before they’re redirected away from Calendly to other websites.”
How to protect yourself against cyberthreats
MacOS users tend to experience fewer malware attacks than PC users. But this idea can make MacOS users more vulnerable to attacks because they may feel they are simply safe. Because hackers are getting more and more sophisticated, it’s important never to let your guard down and to follow these precautions.
Be cautious with links: If you receive a Calendly link from an unfamiliar sender, refrain from clicking on any embedded links, even if the sender appears trustworthy. Additionally, exercise vigilance when dealing with phishing emails or messages related to crypto exchanges or wallets, as they may contain malicious attachments or links with malware. When using Calendly, take note of the source and domain of any links you encounter on the interface. Before clicking, hover your mouse over the text to verify the link address and avoid accessing potentially harmful phishing links.
Send meeting links yourself: Whenever possible, send the meeting link directly to the person scheduling the call. This minimizes the risk of accidentally clicking on malicious links.
Have good antivirus software: The best way to protect yourself from clicking malicious links that install malware that may get access to your private information is to have antivirus protection installed on all your devices. This can also alert you of any phishing emails or ransomware scams. Get my picks for the best 2024 antivirus protection winners for your Mac, Windows, Android & iOS devices.
Perform regular updates: Regularly update your operating system and security software to stay ahead of potential vulnerabilities.
Have strong passwords and use two-factor authentication: Using the same password across multiple platforms will always make you more vulnerable because if one account gets hacked, they all get hacked. And two-factor authentication is just an extra shield that will prevent a hacker from getting into your accounts. Make sure to use a password manager to keep track of all your passwords.
Person typing on a laptop (Kurt “CyberGuy” Knutsson)
MORE: DON’T FALL FOR THESE SNEAKY TAX SCAMS THAT ARE OUT TO STEAL YOUR IDENTITY AND MONEY
Kurt’s key takeaways
As long as there is money and information to steal online, hackers will stop at nothing to trick innocent people into downloading malware onto their devices. So, stay up to date with the latest threats so that you can ensure you’re doing everything to protect yourself.
Have you encountered suspicious meeting requests via Calendly or other scheduling apps? Do you think the app companies should do more to verify the authenticity of such links? Let us know by writing us at Cyberguy.com/Contact.
For more of my tech tips & security alerts, subscribe to my free CyberGuy Report Newsletter by heading to Cyberguy.com/Newsletter.
Ask Kurt a question or let us know what stories you’d like us to cover.
Answers to the most asked CyberGuy questions:
Copyright 2024 CyberGuy.com. All rights reserved.