Attention iPhone owners: A serious cyberthreat is targeting Apple IDs, and it’s more crucial than ever to be on your guard. Security experts from Symantec have uncovered a sophisticated SMS phishing campaign designed to trick you into giving up your valuable Apple ID credentials.
GET SECURITY ALERTS, EXPERT TIPS – SIGN UP FOR KURT’S NEWSLETTER – THE CYBERGUY REPORT HERE
The mechanics of the attack
Here’s how the scam works: hackers send out text messages that look like they’re from Apple. These messages urgently request that you click on a link for an important iCloud update or verification. Symantec’s research shows these links lead to cleverly designed fake websites that ask for your Apple ID and password. To make the site seem legitimate, the attackers have even included a CAPTCHA.
Once you complete the CAPTCHA, you’re taken to what looks like an outdated iCloud login page, where you’re prompted to enter your credentials. This information is gold for cybercriminals because it grants them access to your personal and financial data and control over your devices.
Below is an email version of this same scam to avoid. Note the strange email return address originating from a non-Apple account, riddled with dashes and strange characters.
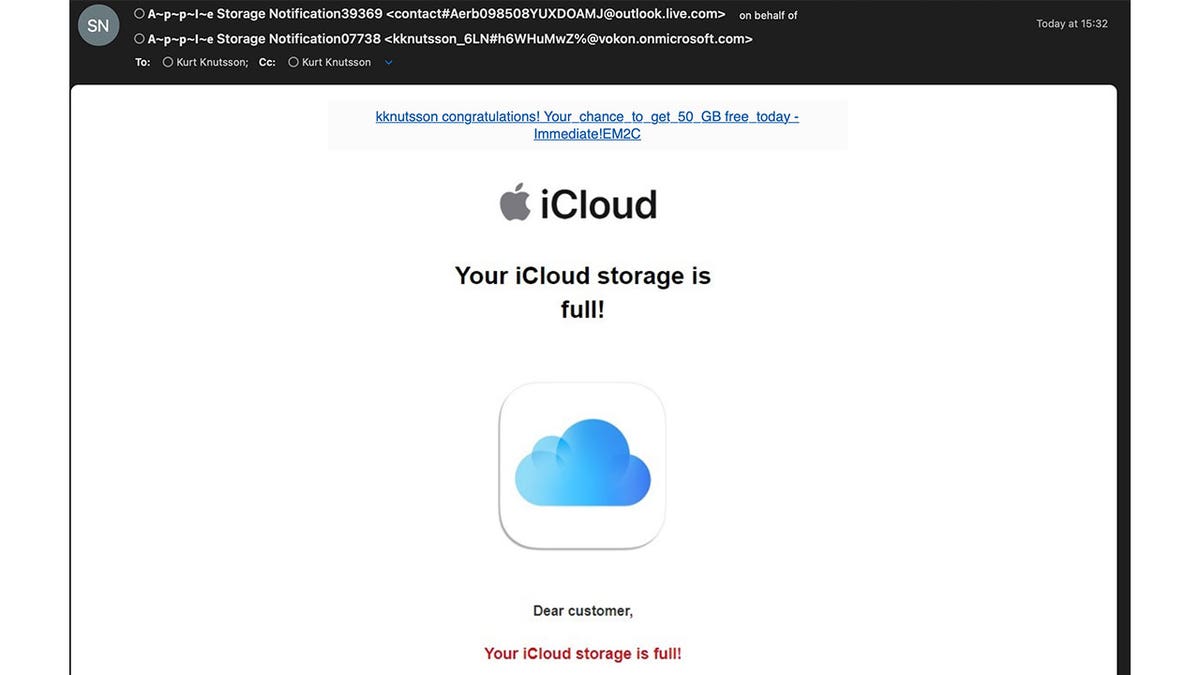
The email scam can claim that a user’s iCloud storage is full. (Kurt “CyberGuy” Knutsson)
Apple’s response and protective measures
Apple is aware of these tactics and has guidelines to help you stay protected. First and foremost, enable two-factor authentication on your Apple ID. This adds an extra layer of security by requiring a password and a six-digit verification code whenever you log in from a new device.
Remember, Apple will never ask you to disable security features like two-factor authentication or Stolen Device Protection. Scammers might claim this is necessary to resolve an issue, but it’s a trap designed to lower your defenses.

An iPhone scam uses text messages. (Kurt “CyberGuy” Knutsson)
Spotting phishing attempts
Phishing scams can be sneaky, but there are ways to identify them. Look closely at the URLs in any suspicious messages. Although the message might appear legitimate, the web address usually won’t match Apple’s official site. Also, be wary of any text that deviates from Apple’s typical communication style.
Symantec highlighted a specific phishing message as part of their warning on July 2. The fraudulent SMS read: “Apple important request iCloud: Visit signin[.]authen-connexion[.]info/iCloud to continue using your services.” Odd characters and unfamiliar domains are clear indicators of a scam.

iPhone users should enable two-factor authentication on their Apple ID. (Kurt “CyberGuy” Knutsson)
Broader scam tactics and how to avoid them
These phishing attempts aren’t just targeting Apple users. People have reported receiving messages similar to those from companies like Netflix and Amazon, claiming account issues or expired credit cards. These messages also direct you to click a link and enter your personal information.
The Federal Trade Commission advises that legitimate companies will never request sensitive information via text. If you receive a message like this, contact the company directly using a verified number or website, not the information provided in the text.
How to protect yourself from Apple text and email scams
1) Always use strong antivirus protection on all your devices
This is perhaps one of the best investments you can make for yourself to protect yourself from phishing scams. Having antivirus software actively running on your devices will make sure you are stopped from clicking on any malicious links or from downloading any files that will release malware into your device and potentially have your private information stolen. Read my review of my best antivirus picks here.
2) Don’t take the bait
Scammers often use alarming language to provoke immediate action. Phrases like “act now” or “important” are red flags. Stay calm and skeptical of any unsolicited messages.
3) Enable two-factor authentication on your Apple devices
Implementing multifactor authentication on your Apple ID can greatly enhance your security. Always verify the source of messages that claim to be from Apple. If you’re unsure, manually log into your account through the official Apple website or your iPhone settings instead of clicking any links.
4) Keep software up to date
Regularly update your operating system, web browsers and antivirus software to ensure they are equipped to detect and prevent the latest threats. You can regularly check for these updates on your device’s settings app for software updates, and you can go to your App Store or Google Play Store (depending on the device you have) to check for updates on individual apps. Follow these steps here.
2 BULLETPROOF STEPS TO HACK-PROOF YOUR MAC
What should you do if you’ve clicked a link and installed malware on your device?
If you’ve been hacked, it’s not too late. There are several ways you can protect yourself from hackers, even when they have access to your information.
1) Scan your device for malware
First, you’ll want to scan your computer with a reputable and legitimate antivirus program. See my expert review of the best antivirus protection for your Windows, Mac, Android and iOS devices.
2) Change your passwords immediately
If you’ve inadvertently given your information to hackers or malicious actors, they could have access to your social media or banking accounts. To prevent this, you should change your passwords for all your important accounts as soon as possible. However, you should not do this on your infected device, because the hacker might see your new passwords. Instead, you should use ANOTHER DEVICE, such as your laptop or desktop, to change your passwords. Make sure you use strong and unique passwords that are difficult to guess or break. You can also use a password manager to generate and store your passwords securely.
3) Monitor your accounts and transactions
You should check your online accounts and transactions regularly for suspicious or unauthorized activity. If you notice anything unusual, report it to the service provider or the authorities as soon as possible. You should also review your credit reports and scores to see signs of identity theft or fraud.
4) Use identity theft protection
Phishing emails target your personal information. Hackers can use this information to create fake accounts in your name, access your existing accounts and pretend to be you online. This can cause serious damage to your identity and credit score.
To avoid this, you should use identity theft protection services. These services can track your personal information, such as your home title, Social Security Number, phone number and email address, and notify you if they detect any suspicious activity. They can also help you freeze your bank and credit card accounts to stop hackers from using them.
One of the best parts of using some services is that they might include identity theft insurance of up to $1 million to cover losses and legal fees and a white-glove fraud resolution team where a U.S.-based case manager helps you recover any losses. Read more of my review of the best identity theft protection services here.
5) Contact your bank and credit card companies
If hackers have obtained your bank or credit card information, they could use it to make purchases or withdrawals without your consent. You should contact your bank and credit card companies and inform them of the situation. They can help you freeze or cancel your cards, dispute any fraudulent charges and issue new cards for you.
6) Alert your contacts
If hackers have accessed your email or social media accounts, they could use them to send spam or phishing messages to your contacts. They could also impersonate you and ask for money or personal information. You should alert your contacts and warn them not to open or respond to any messages from you that seem suspicious or unusual.
7) Restore your device to factory settings
If you want to make sure that your device is completely free of any malware or spyware, you can restore it to factory settings. This will erase all your data and settings and reinstall the original version. You should back up your important data before doing this and only restore it from a trusted source.
HOW TO REMOVE YOUR PRIVATE DATA FROM THE INTERNET
Kurt’s takeaways
As cyberattacks become increasingly sophisticated, staying informed and cautious is crucial. Protect your Apple ID and personal information by following Apple’s security guidelines and being wary of unsolicited messages. By taking these precautions, you can safeguard your devices and data from malicious actors.
Have you ever been a victim of a cyberscam? If so, what happened and how did you recover? Let us know by writing us at Cyberguy.com/Contact.
For more of my tech tips and security alerts, subscribe to my free CyberGuy Report Newsletter by heading to Cyberguy.com/Newsletter.
Ask Kurt a question or let us know what stories you’d like us to cover.
Follow Kurt on his social channels:
Answers to the most asked CyberGuy questions:
Copyright 2024 CyberGuy.com. All rights reserved.



